Difference between revisions of "Main Page"
(some refactoring) |
|||
| (32 intermediate revisions by 5 users not shown) | |||
| Line 1: | Line 1: | ||
| − | __NOTOC__ | + | __NOTOC__{{DISPLAYTITLE:explain xkcd}} |
| − | {{DISPLAYTITLE:explain xkcd}} | ||
| − | |||
<center> | <center> | ||
| − | |||
| − | We have | + | <font size=5px>''Welcome to the '''explain [[xkcd]]''' wiki!''</font><br> |
| − | <!-- Note: the - | + | We have an explanation for all [[:Category:Comics|'''{{#expr:{{PAGESINCAT:Comics|R}}-13}}''' xkcd comics]], |
| − | + | <!-- Note: the -13 in the calculation above is to discount subcategories (there are 8 of them as of 2013-02-27), | |
| − | and only | + | as well as [[List of all comics]] and the pages it has been split across, which are obviously not comic pages. |
| − | ({{#expr: | + | The extra one difference corresponds to 404, which is not really a comic, even though we've categorised it so. |
| − | + | --> | |
| + | and only {{PAGESINCAT:Incomplete articles|R}} | ||
| + | ({{#expr: {{PAGESINCAT:Incomplete articles|R}} / {{LATESTCOMIC}} * 100 round 0}}%) [[:Category:Incomplete articles|are incomplete]]. Help us finish them! | ||
</center> | </center> | ||
| − | |||
== Latest comic == | == Latest comic == | ||
| − | |||
<div style="border:1px solid grey; background:#eee; padding:1em;"> | <div style="border:1px solid grey; background:#eee; padding:1em;"> | ||
<span style="float:right;">[[{{LATESTCOMIC}}|'''Go to this comic explanation''']]</span> | <span style="float:right;">[[{{LATESTCOMIC}}|'''Go to this comic explanation''']]</span> | ||
| Line 26: | Line 23: | ||
== New here? == | == New here? == | ||
| − | You can read a brief introduction about this wiki at [[explain xkcd]]. Feel free to sign up for an account and contribute to the wiki! | + | <div style="float:right; margin: 0 0 1em 1em">{{Special:ContributionScores/10/7/nosort,notools}}<div style="font-size:0.85em; width:25em; font-style:italic">[[Special:ContributionScores|Lots of people]] contribute to make this wiki a success. Many of the recent contributors, listed above, have just joined. You can do it too! Create your account [[Special:UserLogin/signup|here]].</div></div> |
| + | |||
| + | You can read a brief introduction about this wiki at [[explain xkcd]]. Feel free to sign up for an account and contribute to the wiki! We need explanations for comics, characters, themes, memes and everything in between. If it is referenced in an [[xkcd]] web comic, it should be here. | ||
| + | |||
| + | *If you're new to wikis like this, take a look at these help pages describing [[mw:Help:Navigation|how to navigate]] the wiki, and [[mw:Help:Editing pages|how to edit]] pages. | ||
| + | |||
| + | *Discussion about various parts of the wiki is going on at [[Explain XKCD:Community portal]]. Share your 2¢! | ||
| − | * | + | *[[List of all comics]] contains a table of most recent xkcd comics and links to the rest, and the corresponding explanations. There are incomplete explanations listed [[:Category:Incomplete articles|here]]. Feel free to help out by expanding them! |
| − | * | + | *If you see that a new comic hasn't been explained yet, you can create it: '''[[Help:How to add a new comic explanation|Here's how]]'''. |
| − | * [[ | + | *We sell advertising space to pay for our server costs. To learn more, go [[explain xkcd:Advertise Here|here]]. |
== Rules == | == Rules == | ||
| − | Don't be a jerk. | + | Don't be a jerk. There are a lot of comics that don't have set in stone explanations; feel free to put multiple interpretations in the wiki page for each comic. |
If you want to talk about a specific comic, use its discussion page. | If you want to talk about a specific comic, use its discussion page. | ||
| − | Please only submit material directly related to —and helping everyone better understand— xkcd... and of course ''only'' submit material that can legally be posted (and freely edited. | + | Please only submit material directly related to —and helping everyone better understand— xkcd... and of course ''only'' submit material that can legally be posted (and freely edited). Off-topic or other inappropriate content is subject to removal or modification at admin discretion, and users who repeatedly post such content will be blocked. |
| − | If you need assistance from an admin, | + | If you need assistance from an [[explain xkcd:Administrators|admin]], post a message to the [[explain xkcd:Community portal/Admin requests|Admin requests]] board. |
[[Category:Root category]] | [[Category:Root category]] | ||
Revision as of 01:59, 30 October 2013
Welcome to the explain xkcd wiki!
We have an explanation for all 2 xkcd comics,
and only 0
(0%) are incomplete. Help us finish them!
Latest comic
Explanation
| |
This explanation may be incomplete or incorrect: Created by CREEPING TENDRILS OF STARCH - Please change this comment when editing this page. Do NOT delete this tag too soon. |
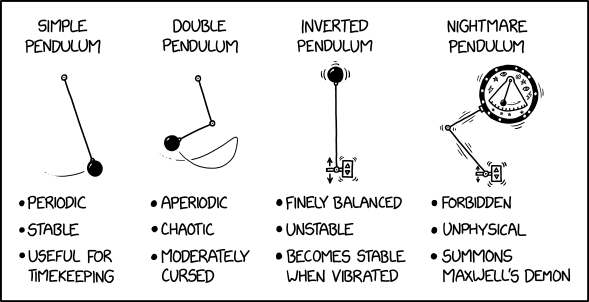
This comic shows and describes several pendulums. The first three are actual physics models, while the last one is made up for absurdity. This is a recurring format of xkcd comics, as shown in 2289: Scenario 4.
The simple pendulum consists of a joint, rod, and weight, and when released (inside a gravity field or other accelerating force), it swings in a regular fashion. The "period" of a pendulum is the amount of time it takes to complete one cycle, swinging back and forth. In a simple pendulum, the period is consistent, predictable, and depends primarily on the length of the pendulum (being largely independent of both mass and length of arc). This predictability makes pendulums useful in applications such as timekeeping, where the earliest accurate clocks (such as a grandfather clock) made use of pendulums as regulators.
The double pendulum consists of 2 joints, 2 rods, and a weight, and when released, it swings in a chaotic fashion. Interestingly, this follows by the mathematical definition of chaotic, being that small changes in initial conditions result in vast differences in end results. This pendulum is thus nearly unpredictable, and due to this chaotic nature, real life applications are very limited.
The inverted pendulum consists of a simple pendulum that is placed upside down, with some apparatus underneath vibrating it vertically to keep it upwards. If left unpowered (or improperly controlled from positional feedback) it will fall, hence the "unstable" part. (The comic, however, appears to depict Kapitza's pendulum, a powered version that does not rely upon monitoring and feedback control.)
The nightmare pendulum appears to be an inverted double pendulum, with an additional uninverted pendulum swinging within its much more substantial weight (which is also adorned with archaic/mystical symbols). The comic claims that this pendulum summons Maxwell's demon, jokingly implying that Maxwell’s demon is an actual entity. In fact, Maxwell's demon is a thought experiment in which a being (the demon) is posted at a tiny door between two gas vessels. It lets only slow-moving (cold) gas molecules move in one direction, and only fast-moving (hot) ones in the other direction. One vessel would thus gradually become hot and the other cold, appearing to violate the second law of thermodynamics. However, it doesn't, but the thought experiment has stimulated much discussion since it was first proposed by James Clerk Maxwell in 1867.
The title text continues this joke explicitly, by referencing a real paper titled Vibro-levitation and inverted pendulum: parametric resonance in vibrating droplets and soft materials and implying that the paper ties the "creepy fingers" produced in this way to Maxwell's demon. The paper only actually suggests that the phenomenon is related to inverted pendulum dynamics. This gives a humorous example for the abuse of citations. Technically, the cited reference only supports the claim immediately before it, that the behavior of a cornstarch-water mix (also known as oobleck) can be modeled as inverted pendulums. But by proximity the reference also seems to support the part about Maxwell's Demon. The illusion is helped by the description of the cornstarch as creepy, which is added in the beginning without any visible separation from the actual content of the citation.
Transcript
- [Four types of pendulums are shown in a single panel. Each has a bullet list below the depiction.]
- [Label:]
- Simple pendulum
- [A basic pendulum consisting of a joint, rod, and weight swinging in a regular arc]
- Periodic
- Stable
- Useful for timekeeping
- [Label:]
- Double pendulum
- [A pendulum consisting of 2 joints, 2 rods, and a weight swinging in a more loopy arc]
- Aperiodic
- Chaotic
- Moderately cursed
- [Label:]
- Inverted pendulum
- [An upside-down basic pendulum with some apparatus underneath vibrating up and down]
- Finely balanced
- Unstable
- Becomes stable when vibrated
- [Label:]
- Nightmare pendulum
- [An inverted double pendulum, with an additional uninverted pendulum swinging within a large weight adorned with archaic/mystical symbols]
- Forbidden
- Unphysical
- Summons Maxwell's Demon
Is this out of date? .
New here?
Last 7 days (Top 10) |
|||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
You can read a brief introduction about this wiki at explain xkcd. Feel free to sign up for an account and contribute to the wiki! We need explanations for comics, characters, themes, memes and everything in between. If it is referenced in an xkcd web comic, it should be here.
- If you're new to wikis like this, take a look at these help pages describing how to navigate the wiki, and how to edit pages.
- Discussion about various parts of the wiki is going on at Explain XKCD:Community portal. Share your 2¢!
- List of all comics contains a table of most recent xkcd comics and links to the rest, and the corresponding explanations. There are incomplete explanations listed here. Feel free to help out by expanding them!
- If you see that a new comic hasn't been explained yet, you can create it: Here's how.
- We sell advertising space to pay for our server costs. To learn more, go here.
Rules
Don't be a jerk. There are a lot of comics that don't have set in stone explanations; feel free to put multiple interpretations in the wiki page for each comic.
If you want to talk about a specific comic, use its discussion page.
Please only submit material directly related to —and helping everyone better understand— xkcd... and of course only submit material that can legally be posted (and freely edited). Off-topic or other inappropriate content is subject to removal or modification at admin discretion, and users who repeatedly post such content will be blocked.
If you need assistance from an admin, post a message to the Admin requests board.