Difference between revisions of "Main Page"
(→New here?: fix link) |
|||
| (5 intermediate revisions by one other user not shown) | |||
| Line 29: | Line 29: | ||
*If you're new to wikis like this, take a look at these help pages describing [[mw:Help:Navigation|how to navigate]] the wiki, and [[mw:Help:Editing pages|how to edit]] pages. | *If you're new to wikis like this, take a look at these help pages describing [[mw:Help:Navigation|how to navigate]] the wiki, and [[mw:Help:Editing pages|how to edit]] pages. | ||
| − | *Discussion about various parts of the wiki is going on at [[ | + | *Discussion about various parts of the wiki is going on at the [[explain xkcd:Community portal|Community portal]]. Share your 2¢! |
*[[List of all comics]] contains a table of most recent xkcd comics and links to the rest, and the corresponding explanations. There are incomplete explanations listed [[:Category:Incomplete explanations|here]]. Feel free to help out by expanding them! | *[[List of all comics]] contains a table of most recent xkcd comics and links to the rest, and the corresponding explanations. There are incomplete explanations listed [[:Category:Incomplete explanations|here]]. Feel free to help out by expanding them! | ||
| Line 43: | Line 43: | ||
If you need assistance from an [[explain xkcd:Administrators|admin]], post a message to the [[explain xkcd:Community portal/Admin requests|Admin requests]] board. | If you need assistance from an [[explain xkcd:Administrators|admin]], post a message to the [[explain xkcd:Community portal/Admin requests|Admin requests]] board. | ||
| − | |||
| − | |||
[[Category:Root category]] | [[Category:Root category]] | ||
Revision as of 17:59, 4 March 2014
Welcome to the explain xkcd wiki!
We have an explanation for all 2 xkcd comics,
and only 5
(0%) are incomplete. Help us finish them!
Latest comic
Explanation
| |
This explanation may be incomplete or incorrect: Created by a GUIDED MISSILE THAT MISSED THE TARGET DUE TO COORDINATE DRIFT - Please change this comment when editing this page. Do NOT delete this tag too soon. |
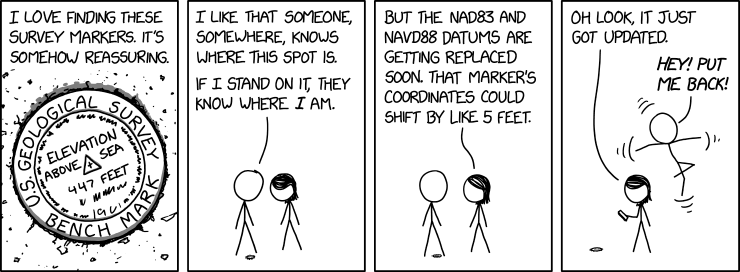
Cueball and Megan have found a survey marker on the ground. Survey markers such as these are used as reference points for the NAD 83 and NAVD 88 geodetic reference systems, and the U.S. National Geodetic Survey has a database storing the coordinates of these markers. However, those two systems are being replaced by the New Datums of 2022 (delayed to 2024-2025), which is primarily based on satellite systems and gravimetric models.
When they update the database in the comic, Cueball's position, both horizontal and vertical, changes to compensate, leaving him panicking in mid-air. In reality, updating a database to change the coordinates of a location would not physically move items at the location.[citation needed] Arguably, if they did, no-one would much notice, since everything surrounding them should similarly move simultaneously to its corrected position as well. However, in the comic, the only things whose position is 'known' (and can therefore be 'corrected') are those that are directly on a marker, hence why this shifting does not seem to apply to Megan.
The title text refers to NAD 83 being around 7 feet off. This probably refers to the 7 foot difference in the positioning of the centres of the notional Earth ellipsoids used as the basis for NAD 83 and WGS84.
Absurd outcomes from differing survey standards was also the topic of 2888: US Survey Foot.
Transcript
- [Zoomed in view of a round marker on the ground, with small specks of dirt around it. There is one line of text going around the central part in the outer rim of the marker, with the first three words written around the top, and the last two words written around the bottom (thus not text that are going all the way around in one single line). Inside this rim there are more text on three lines. In the center there is a small cross in a triangle pointing up in relation to the central text. There are more unreadable text below the last line of text and around the inner part of the rim. And off panel voice, which in the next panel turns out to be Cueball, is written above the mark.]
- U.S. Geological Survey bench mark
- Elevation above sea 447 feet
- Cueball (off-panel): I love finding these survey markers. It's somehow reassuring.
- [Cueball and Megan are shown as they look down on the marker. Cueball has one leg on either side of the marker and Megan stands to the right.]
- Cueball: I like that someone, somewhere, knows where this spot is.
- Cueball: If I stand on it, they know where I am.
- [Cueball and Megan looks up at each other.]
- Megan: But the NAD83 and NAVD88 datums are getting replaced soon. That marker's coordinates could shift by like 5 feet.
- [Megan is looking down at her phone in her hand, standing in the same place in relation to the marker. Cueball is now floating in the air behind her 5 feet above the ground, while flailing with his arms and legs (as shown with three small curved lines at the end of either arm and above and below him.)]
- Megan: Oh look, it just got updated.
- Cueball: Hey! Put me back!
Is this out of date? .
New here?
Last 7 days (Top 10) |
|||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
You can read a brief introduction about this wiki at explain xkcd. Feel free to sign up for an account and contribute to the wiki! We need explanations for comics, characters, themes, memes and everything in between. If it is referenced in an xkcd web comic, it should be here.
- If you're new to wikis like this, take a look at these help pages describing how to navigate the wiki, and how to edit pages.
- Discussion about various parts of the wiki is going on at the Community portal. Share your 2¢!
- List of all comics contains a table of most recent xkcd comics and links to the rest, and the corresponding explanations. There are incomplete explanations listed here. Feel free to help out by expanding them!
- We sell advertising space to pay for our server costs. To learn more, go here.
Rules
Don't be a jerk. There are a lot of comics that don't have set in stone explanations; feel free to put multiple interpretations in the wiki page for each comic.
If you want to talk about a specific comic, use its discussion page.
Please only submit material directly related to —and helping everyone better understand— xkcd... and of course only submit material that can legally be posted (and freely edited). Off-topic or other inappropriate content is subject to removal or modification at admin discretion, and users who repeatedly post such content will be blocked.
If you need assistance from an admin, post a message to the Admin requests board.