Difference between revisions of "1755: Old Days"
(→Table) |
(→Table of statements) |
||
| Line 33: | Line 33: | ||
|- | |- | ||
|C++ was big because it supported floppy disks. It still just punched holes in them|| | |C++ was big because it supported floppy disks. It still just punched holes in them|| | ||
| − | |||
==Transcript== | ==Transcript== | ||
Revision as of 10:12, 4 November 2016
| Old Days |
 Title text: Lot of drama in those days, including constant efforts to force the "Reflections on Trusting Trust" guy into retirement so we could stop being so paranoid about compilers. |
Explanation
| |
This explanation may be incomplete or incorrect: More explanation required. Explain statements in table. If you can address this issue, please edit the page! Thanks. |
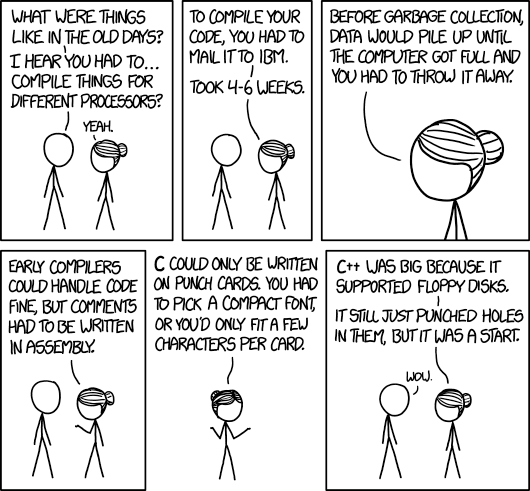
This comic is showing a coversation between Cueball and Hairbun about computer programming in the past. Hairbun explains how tough it was for programmers to write and create code in the past. While the initial explanation that code needed to be compiled for multiple architectures is correct, Hairbun's claims rapidly grow ridiculous. (i.e. even old floppy disks weren't hole-punch based.)
As usual in XKCD, conversation becomes more and more improbable.
The title text refers to this famous 1984 paper by UNIX co-creator Ken Thompson in which he described a way to hide a virtually undetectable backdoor in the UNIX login code via a second backdoor in the C compiler.
Using the technique in his paper, it would be impossible to discover the hacked login by examining the official source code for either the login or the compiler itself. Ken Thompson may have actually included this backdoor in early versions of UNIX, undiscovered.
Ken Thompson's paper demonstrated that it was functionaly impossible to prove that any piece of software was fully trustworthy. Hairbun claims that the solution was to wait for Ken Thompson himself to retire. In reality, any coder who created the first version of a compiler (or a similar critical component) could inject a similar backdoor into software. Though the problem was (claimed to) be solved in David A. Wheeler PhD dissertation "Fully Countering Trusting Trust through Diverse Double-Compiling (DDC)".
Table of statements
| |
This explanation may be incomplete or incorrect: Need to fill out explanations If you can address this issue, please edit the page! Thanks. |
| Compile things for different processors | |
| Mail it to IBM...Took 4-6 weeks | |
| Data would pile up until the computer got full and you had to throw it away | Actually, even in the old days, you could delete things without garbage collection |
| Compilers could handle code fine, but comments had to be written in assembly. | |
| C could only be written on punch cards...Using a compact font | |
| C++ was big because it supported floppy disks. It still just punched holes in them |
Transcript
DiscussionReflections on Trusting Trust (pdf), Ken Thompson's acceptance speech for the 1984 Turing Award, in which he discusses creating a backdoor in the C compiler (yes, there was only 1 when he invented the language) that itself creates a second backdoor in the login program when it is compiled. Additionally, it reproduces itself when compiling the C compiler from un-tampered-with source code, so that anyone using the binary (compiled) compiler would be unable to avoid reproducing the backdoor in all its forms. This is the sort of thing that gives security programmers nightmares. 108.162.221.168 04:52, 4 November 2016 (UTC) (bonsaiviking) The "4-6 weeks" thing might be a reference to high-performance computing, in particular scientific calculations, a few decades back. From what I've heard from older people in my scientific field (I'm too young to have experienced it myself), you'd prepare your program on punch cards, mail these to an institution owning a fast computer (because your group or university didn't have one), and they'd run the program and mail the result back to you. This, I've been told, took a few weeks. Maybe someone with first-hand experience can give more information. 141.101.104.98 10:34, 4 November 2016 (UTC)
Source Code on Punched Cards: As an undergrad at Durham Uni I remember punching PL1 source code onto cards to be inserted into a batch queue to be compiled and run on an IBM360 at the nearby city of Newcastle, overnight. 141.101.98.160 11:57, 4 November 2016 (UTC) At the risk of emulating Dilbert's "Topper", I remember at school writing programs on coding sheets (effectively squared paper; one character in each box), which would get sent to the local university, where they would be punched onto cards and run on the mainframe. The following week, you'd get your coding sheets back, plus the cards and the printout from your batch job. Then you'd make your corrections, also on coding sheets... 141.101.98.143 13:35, 4 November 2016 (UTC) I'm reminded of Frank Hayes' song, "When I Was a Boy": "And we programmed in ones and in zeroes / And sometimes we ran out of ones!" On a more serious note, C came out in the late seventies, and I was using punch cards as late as 1975. That's not "long" before, and I wouldn't be too surprised if there were C compilers that accepted punched card input. Gmcgath (talk) 12:27, 4 November 2016 (UTC)
Is there a parallel here between computing and real life? For example, panel 3 mimics real life garbage collection, where you let your trashcan pile up before collection. Similarly, without texting in the 'old days' you would have had to mail stuff to people whereas to do things we can do in seconds now. So she's using his views of the -- ExplainBot (talk) (please sign your comments with ~~~~) I think the punched cards explanation is missing the point that C (or any language, that I know) didn't _require_ that it be on punched cards. I.e. there was nothing in the language specification that prohibited the program from being on paper tape, mag tape, disk, etc. 162.158.74.70 14:22, 4 November 2016 (UTC)Pat Is it just me, or is there a parallel between sending you code off to be compiled and sending your code off to an app store. In both cases a required part of the build is sending your code off to a private company for approval. Olleicua (talk) 15:28, 4 November 2016 (UTC) Can someone please verify that it is "actually very difficult" to punch holes in floppy disks? Probably it should be attempted on at least 1000 different disks of different kinds to make sure. 162.158.75.64 (talk) (please sign your comments with ~~~~) Interesting: there exist two versions of this comic with different size https://imgs.xkcd.com/comics/old_days.png and https://imgs.xkcd.com/comics/old_days_2x.png The latter is used when zooming in on the comic's page --172.68.51.70 19:48, 4 November 2016 (UTC)
You didn't have to ship the punch cards to a company, but you did have to put them into a queue to be processed, and if you did have a typo or other simple mistake, you'd have to wait to get the output before knowing (which could take days). Most of what she says actually makes sense, it's just not fully accurate. You use to have to manually collect your garbage (making sure you unallocated your memory). You often did have to mix code and assembly (thought not for comments, and would that be // or /* */ or # or...). She also follows computer storage history. So again, not accurate, but it makes sense. 108.162.237.88 19:56, 4 November 2016 (UTC)
Is there a parallel here between real life and computing? Panel 3 is like the way people wait until their trashcan's full before throwing it out, and panel 2 could reference how you had to mail things to people in the 'old days' instead of texting them, which takes no time nowadays. So, she's using the things he knows were true in the past (such as texting not existing) to make ridiculous statements which sound believable to him. Not sure about the other panels though. ExplainBot (talk) 15:39, 5 November 2016 (UTC) Back in my day, we lived RFC 1149. Y'all got it easy now. *scoff* --172.68.78.133 13:37, 6 November 2016 (UTC) ... and when we got home, our Dad would kill us, and dance about on our graves singing "Hallelujah." :-D --162.158.88.254 17:34, 6 November 2016 (UTC) It is not clear to me that the final 'Wow' indicates that Cueball falls for it. Other interpretations include surprise that Hairbun cares so little or that she would go so far, or shock that she thinks so little of Cueball or indignity that she cares so little for his (admittedly ageist) social overture. 162.158.69.160 18:39, 7 November 2016 (UTC) ....I'm 17 and fell for this completely. I feel naive. 162.158.167.168 10:43, 7 January 2017 (UTC) |
