1181: PGP
| PGP |
 Title text: If you want to be extra safe, check that there's a big block of jumbled characters at the bottom. |
Explanation
PGP (or GnuPG for the free, open source version) is a program which can be used to encrypt and sign data, including messages sent as emails. It is often used in combination with email software extensions, such as Enigmail (for Thunderbird). Encrypting the message would prevent anybody from reading it if they didn't have the key to decrypt. Signing the message would mean that the message can be verified as unaltered, if the reader was to check the message against the signature. People who use such a program typically only use the feature to sign the message, since encrypting it (which would give you the privacy) requires that the recipient already be a PGP user. Hence the irony here is that nobody actually verifies the "signature" either, but feel secure that the message appears to be signed.
PGP or Pretty Good Privacy, uses Public-key cryptography, which is defined in RFC4880. The blob which makes the signature is a binary (clear sign) signature which is encoded into ASCII using ASCII armor.
The use of signing software for email is so rare that most people have never seen a signed message. The joke here is that because of that, nobody ever tries to spoof a PGP header. So if you see one, it's likely to be authentic. This ignores actual privacy guarantees PGP provides, therefore giving a false sense of security.
A similar thing happens on some web pages that simply state "This page is secure" or include the padlock icon in the body of the page, and then ask for your credit card information, while not actually using SSL (and showing that little padlock or an "https"). (Read an old blog/rant about the padlock icon and security).
This irresponsible approach to security is unfortunately quite common with users and even more so for computer security related topics. When confronted with something strange (like the blob at the bottom) most people simply believe it: If it says it's secure it really has to be - even if it actually isn't.
Many security geeks would be quite annoyed by this ignorant behavior.
Transcript
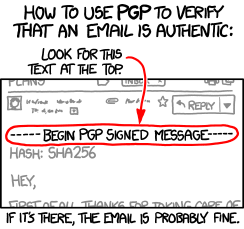
- How to use PGP to verify that an email is authentic:
- Look for this text at the top
- [In mail header, light grey.] Reply
- -----BEGIN PGP SIGNED MESSAGE-----
- [in mail message, light grey]
- HASH: SHA256
- Hey,
- First of all, thanks for taking care of
- [After mail message]
- If it's there, the email is probably fine
Discussion
Everybody below seems to have misread the comic. It says nothing about 'verifying that the email is secure' or secret, or encrypted. It says verifying that the email is AUTHENTIC. This is a significant difference in meaning.24.70.188.179 15:55, 4 March 2013 (UTC)
- I understood the same. I am probably the only nerd that use PGP. So if you receive a mail with that "heading" it's probably from me.83.42.5.246 09:20, 5 March 2013 (UTC)
- "AUTHENTIC" what? Not to be too much of an engineer, but a confirmed/verified PGP signature only means that the contents have not been altered and the message was signed by the stated someone, but that 'stated someone' isn't necessarily the person whom you think it is. To map a real person to a digital signature PGP uses the "Web of Trust" model that relies upon the signer and reader trusting many third parties and thus building trust-links (a web)... rather than a central authority figure who issues trust to both users (the PKI model).--Sweerek (talk) 15:28, 2 April 2013 (UTC)
- Or you could go see them in person and have them print out their signature. That's right, Jacky720 just signed this (talk | contribs) 19:22, 2 July 2017 (UTC)
I don't really understand what's funny about this comic. 76.106.251.87 05:53, 4 March 2013 (UTC)
- Perhaps the fact that an email is encrypted (or pretends to be) at all? Most emails aren't encrypted, or none of the ones I send or get are. :D 59.10.72.121 06:28, 4 March 2013 (UTC)
- what is funny, is that nobody can read the signatures -- and therefore they a less than pointless, as the gives a false sense of security.
- I always sign my mails. If people cannot verify the signature, they are probably not too aware of security issues anyway. The only problem is windows Live Mail users, who receive an empty body with the original message as an attachment. At least in 2010 it was like that. 46.142.43.161 18:09, 4 March 2013 (UTC)madd
I think merely the fact that PGP is in the email itself suggests the sender of the email is probably just a big nerd and therefore can be trusted. -- 153.90.91.1 (talk) (please sign your comments with ~~~~)
- You are the type of person that the comic is making fun of. You assume it's safe and don't bother to verify it. 108.162.212.18 16:37, 28 June 2014 (UTC)
Isn't it that those markers could very simply just have been typed in, rather than being part of the decryption system? DonGoat (talk) 07:41, 4 March 2013 (UTC)
With public key systems like PGP you need the public key of the other person to verify the authenticity of the message. Most people do not use PGP or do not know how it works or are just lazy. Some of those are convinced enough just by the outer looks of a signed email: The starting block and the jumbled chars at the end. It is like being impressed by a signature per se in real life without knowing what the one of the person you write to looks like. I think the allusion to pretty good is coincidental. Sebastian --178.26.118.249 08:11, 4 March 2013 (UTC)
- Email client is supposed to automatically check the signature and report it's validity in a way which can't be counterfeited. Few if any do. On the other hand, how much do you really want to need the email is signed? Unless it's asking for password or something, which would be suspicious anyway ... (and in that case, you should reply by ENCRYPTED email. By definition, email encrypted with public key of someone you trust posted to attacker should be useless to him).
- Personally, I don't PGP sign my emails because noone I'm regularly writting to would be able to verify the signature. -- Hkmaly (talk) 09:27, 4 March 2013 (UTC)
There is an interesting comparison to do with regular handwritten signature, as this is exactly how people check the authenticity of a handwritten signed document: check for a signature. If there is one, and if there is, even if you never saw a sample of that signature, trust it. However, as with cryptographic signature with an unknown key, this does rely one something: the fact that it is forbidden, and punishable, to counterfeit one's signature, even if it is badly done (as in: write a random signature, hoping that the recipient does not know the real signature of the alleged author). -- Elessar (talk) 09:02, 4 March 2013 (UTC)
- Speaking of not checking handwritten signatures: http://www.zug.com/pranks/credit/ -- 24.72.82.182 21:45, 4 March 2013 (UTC)
I agree with the commenters above me and I think the explanation goes into the wrong direction. This cartoon has nothing to do with encryption, it's only about (cryptographically) signing an e-mail. PGP can do both, but whilst signing is done using your own secret PGP key, for encryption you must have the public key of the recipient, so they must already know how to use PGP (or GnuPG) and have it installed. The cartoon is about people who either do not have PGP installed in their e-mail program or are using a web mailer (like many) that cannot handle cryptographically signed messages. For them, the signature is useless, unless they believe that the mere existence of a signature is a proof that the message is authentic. Oh, and the explanation is wrong on the ASCII armor. If you read the RFC correctly, this separation line is used if you don't have ASCII armored text but plaintext. 128.7.3.55 09:40, 4 March 2013 (UTC)
- You may be confusing "ASCII armored" (which in OpenPGP speak is "a BASE64-encoded version of the signature or encrypted text") with the encoding of the actual data (which may also be BASE64, or it may be Quoted-Nonprintable, or it may be actual plain-text ASCII). This separation line signals that signature will be at the end, and that the mail will not be encoded in PGP-MIME, which pretty much requires that the signature is ASCII armored.195.144.91.202 12:03, 4 March 2013 (UTC)
- At the time of my comment, the explanation said: »[...] Randall suggests that if you just look for "Begin PGP Signed Message" in the message, the assumption that the message is encrypted is "Pretty Good." This holds true as one of the RFC4880-devised plaintext headers for messages with ASCII armor is exactly this text« (emphasis by me), whereas RFC 4880 defines in section "Cleartext Signature Framework" that this header is used for cleartext messages, i.e. explicitly without ASCII armor. The explanation was changed shortly afterwards, so my comment was outdated and apparently confusing. 128.7.3.55 11:48, 7 March 2013 (UTC)
- I also agree that the explanation doesn't really explain the point. PGP does not only provide encryption (which is in some sense privacy), but also authentication. If I publish my public key, anyone can use it to verify an email I signed with my private key. The joke is about what really happens. The text says: "If you find a header, this indicates a signed message. You are pretty safe if you assume the mail is authentic." This is funny, because email signatures are still so uncommon that there actually is no need to fake it. If you fake an email, why faking a signature? Just don't sign it. The image text goes one step further saying that you're safer when you look at the bottom of the mail and look for some weird random characters. This is what the actual signature looks like, but of course, the only way to really authenticate the mail is to use the sender's public key to verify that the random characters are a real signature. --BKA (talk) 12:19, 4 March 2013 (UTC)
PGP, or GPG (even in Windows) now, helps you verify the sender. If the key kept in the registry, or in your public keyring, matches, then the sender is the one known to you as the owner of that key. Of course, that doesn't stop someone from giving you a public key while pretending to be another, then maintaining the masquerade.
Incidentally nearly EVERYONE has seen a public key verified message. Visit any https website, and odds are the web browser not only established a secure channel through asymmetric (public key) encryption, but also verifies the owner of the 'site by checking with places like VeriSign. How many people here have visited their own HTTPS 'site, (while playing around with a server, for instance,) and had their browser pop up a warning about the 'site being unverified? 156.110.38.82 14:50, 4 March 2013 (UTC)
As several others have noted, PGP can be used to encrypt and/or authenticate a message. I'd argue that the latter function is of little utility in the real world, as it solves a problem that few people have (the system itself dates to when e-mail was used very differently, and the expected future use case didn't exactly go as we all imagined). Security nerds would rarely need to authenticate anything that is otherwise unimportant enough to not bother to encrypt; typical end-users often can't even recognize obvious phishes, so unless their OS transparently refused to even display an email from a sender whose key was not in the recipients' keyring (ignoring all the complexity putting it in there entails) they would treat all emails as authentic anyway...which is what they do. E-mail was never designed for security, and nowadays the majority of it is spam, legit-spam, virtual receipts, and the like; there is so much noise now that most people who need secure communications have other vectors for such.
[TL;DR: if you both need and know how to use PGP authentication of plaintext e-mail for important communication, you probably don't send those important things via plaintext e-mail.] 173.161.183.129 18:49, 4 March 2013 (UTC)
Also, Randall's comment that the presence of a signature does not necessarily authenticate the message is reminiscent of 1121: Identity. --213.151.48.139 12:13, 6 March 2013 (UTC)
Hmmm... my take, and I thought I saw someone else hint at this above, is that the PGP decoration leads the unsophisticated reader into a false sense of security. It's akin to that severe-looking envelope marked "For Official Business Only" but coming from some mass mailer making it seem like their solicitation is in fact some official governmental communication. "It's got that on the cover, it must be important. I better find out what it is..." Voila. Mission accomplished. -- IronyChef (talk) 16:25, 9 March 2013 (UTC)
What would have been really funny is if the email content showed an attempt at Nigerian Scam. Abhaysk (talk) 01:06, 12 March 2013 (UTC)
- "As several others have noted, PGP can be used to encrypt and/or authenticate a message. I'd argue that the latter function is of little utility in the real world" :I'd argue the opposite, spoofing an email is trivial, reading someone elses email is somewhat harder. Having a policy of only performing certain actions based on signed mails from known keys makes a lot of sense. 141.101.98.51 13:36, 18 March 2014 (UTC)
The best use of this is to purposely send emails with invalid signatures. No one will ever notice since no one uses PGP. But if someone ever tries to hold you accountable for an email you sent, you can explain how PGP authentication works and prove that your signature is invalid. 108.162.216.190 13:49, 11 March 2015 (UTC)
