Difference between revisions of "1957: 2018 CVE List"
(The last CVE isn't in a public comment box, so it's not a joke about the 4th CVE, but rather self-contained.) |
(→Explanation: tv tropes llink fixed. and 779 would work better for the cheap viagra link.) |
||
| Line 82: | Line 82: | ||
|This refers to a computer meme where replace "cloud" with "other people's computers" must be used in all marketing presentation to CEOs and not computer literate persons to evaluate the security impact of using "Cloud services". Part of the humor here is that "the cloud", in actuality, is simply a term for hosted services, i.e., computers being run by other people (typically businesses that specialize in this type of "Platform As A Service" or "PAAS" service model). Calling "the cloud" as "other people's computers" is, at its core, entirely accurate, though it takes away the business jargon and simplifies the situation in such a way that it might cast doubt on the security, reliability, and general effectiveness of using "cloud" solutions. | |This refers to a computer meme where replace "cloud" with "other people's computers" must be used in all marketing presentation to CEOs and not computer literate persons to evaluate the security impact of using "Cloud services". Part of the humor here is that "the cloud", in actuality, is simply a term for hosted services, i.e., computers being run by other people (typically businesses that specialize in this type of "Platform As A Service" or "PAAS" service model). Calling "the cloud" as "other people's computers" is, at its core, entirely accurate, though it takes away the business jargon and simplifies the situation in such a way that it might cast doubt on the security, reliability, and general effectiveness of using "cloud" solutions. | ||
|- | |- | ||
| − | |A flaw in Mitre's CVE database allows arbitrary code insertion.[[ | + | |A flaw in Mitre's CVE database allows arbitrary code insertion.[[779|[~~CLICK HERE FOR CHEAP VIAGRA~~]]] |
|Mitre's CVE database is the database where all CVE are stored. Attackers, after gaining access to the database via this flaw, add in a typical spam link purporting to offer cheap viagra. | |Mitre's CVE database is the database where all CVE are stored. Attackers, after gaining access to the database via this flaw, add in a typical spam link purporting to offer cheap viagra. | ||
|- | |- | ||
|It turns out Bruce Schneier is just two mischevious kids in a trenchcoat. | |It turns out Bruce Schneier is just two mischevious kids in a trenchcoat. | ||
| − | |Appears in the title text. {{w|Bruce Schneier}} is security researcher and blogger. He was mentioned in the title texts of [[748: Worst-Case Scenario]] and [[1039: RuBisCO]]. The "two kids in a trenchcoat" is a reference to the | + | |Appears in the title text. {{w|Bruce Schneier}} is security researcher and blogger. He was mentioned in the title texts of [[748: Worst-Case Scenario]] and [[1039: RuBisCO]]. The "two kids in a trenchcoat" is a reference to the {{tvtropes|TotemPoleTrench|}}Totem Pole Trench trope. |
| − | |||
== References == | == References == | ||
Revision as of 19:04, 19 February 2018
| 2018 CVE List |
 Title text: CVE-2018-?????: It turns out Bruce Schneier is just two mischevious kids in a trenchcoat. |
Explanation
| |
This explanation may be incomplete or incorrect: Created by HACKING THIS WIKI VIA THE EDIT BOX - The explanation looks like a list. Explain the comic and put the security vulnerabilities in a table. Do NOT delete this tag too soon. If you can address this issue, please edit the page! Thanks. |
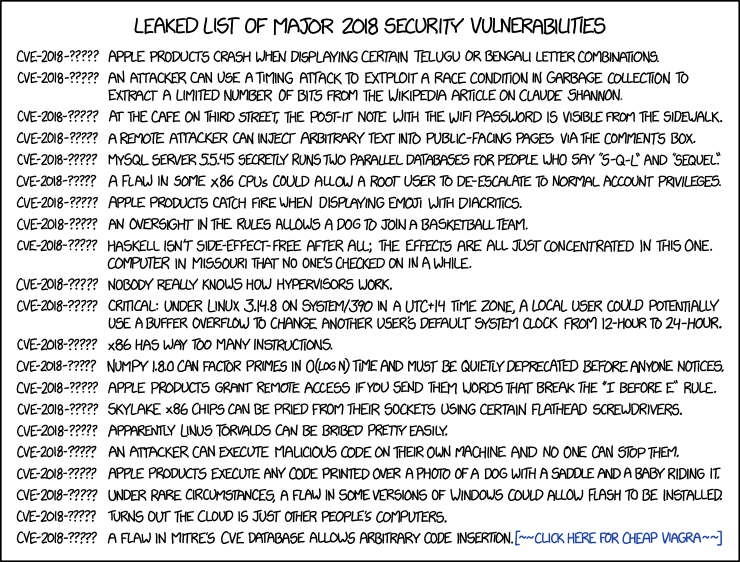
In this comic (released in February 2018), Randall presents a number of spurious predicted CVEs for later in 2018. Each CVE identifier is given as "CVE-2018-?????", reflecting the fact that they have not yet happened so we don't know exactly what their CVE identifier will be.
| Security Vulnerability | Notes |
|---|---|
| Apple products crash when displaying certain Telugu or Bengali letter combinations. | This refers to a real vulnerability in iOS and MacOS publicized a few days before the comic released [1], as well as past similar iOS vulnerabilities[2][3]. |
| An attacker can use a timing attack to extploit [sic] a race condition in garbage collection to extract a limited number of bits from the Wikipedia article on Claude Shannon. | Timing Attack to exploit a race condition in garbage collection refers to Meltdown and Spectre CPU flaws that can be exploited in cloud server like the ones in Wikipedia. Claude Shannon was an early and highly influential information scientist whose work underlies compression, encryption, security, and the theory behind how information is encoded into binary digits - hence the pertinence of extracting just some of the bits from his Wikipedia entry. |
| At the cafe on Third Street, the Post-it note with the WiFi password is visible from the sidewalk. | Writing passwords in a visible place is a major security flaw. For instance, following the 2018 Hawaii false missile alert the agency received criticism for a press photo showing a password written on a sticky note attached to a monitor.[4] However, if a cafe posts their wifi password for customers, this suggests that it's supposed to be public knowledge. However, being visible from outside would allow people to use the wifi without ever entering the building or purchasing anything. |
| A remote attacker can inject arbitrary text into public-facing pages via the comments box. | Describes a common feature on news sites or social media sites like Facebook. The possibility for users to "inject" text into the page is by design. This is a humorous reference to the relatively common security vulnerability "persistent cross-site scripting", where input provided by the user is displayed to other users in a dangerous fashion that allows attackers to inject arbitrary HTML or Javascript code into e.g. a comment section. It might also be a humorous reference to the events before, during and after the 2016 US Presidential elections where Internet Research Agency employees based remotely in St. Petersburg, Russia, but disguised as US citizens, "injected" arbitrary text in the form of political propaganda into comments on multiple web sites, according to an indictment returned by a federal grand jury on February 16, 2018. |
| MySQL server 5.5.45 secretly runs two parallel databases for people who say "S-Q-L" and "sequel." | Some people pronounce "SQL" like "sequel", after SQL's predecessor "SEQUEL (Structured English Query Language)". The standard for SQL suggests that it should be pronounced as separate letters; however, the author of SQL pronounces it "sequel", so the debate is persisting (with even more justification than arguments about how to pronounce "GIF"). MySQL is an open-source relational database management system, the latest GA version (at the time of writing) is MySQL 5.7. |
| A flaw in some x86 CPUs could allow a root user to de-escalate to normal account privileges. | Privilege escalation refers to any illegitimate means of giving a system user greater privilege than they are supposed to have, and most hackers will seek to achieve this if they can. The most highly-sought privilege is that of the root user, which allows complete access to an entire system.
This CVE, however, presents the reverse situation; that a flaw can allow a root user to de-escalate, the exact opposite of what a hacker would want to achieve.[citation needed] (In any case, the root user can always de-escalate manually if they so choose, as they have complete control). |
| Apple products catch fire when displaying emoji with diacritics. | Diacritics are the accents found on letters in some languages (eg. č, ģ ķ, ļ, ņ, š, ž). These would not be found on emojis. It is also a reference to a common problem of modern gadgets catching fire (usually related to flaws in Lithium-Ion batteries). |
| An oversight in the rules allows a dog to join a basketball team. | This likely refers to the movie Air Bud. It is a movie about a dog playing basketball. This has been a common theme in xkcd comics, see 115: Meerkat, 1439: Rack Unit, 1819: Sweet 16, 1552: Rulebook |
| Haskell isn't side-effect-free after all; the effects are all just concentrated in this one. computer [sic] in Missouri that no one's checked on in a while. | Haskell is a functional programming language, functional programming is characterized by using functions that don't have side effects in other parts of the program. The joke here is discovering that indeed it does have side-effects, but for some unknown (and highly absurd) reason they only manifest on a specific computer in a nondescript location, but no one has noticed. |
| Nobody really knows how hypervisors work. | "Hypervisors" are a tool for computer virtualization. Virtualization is an extremely complex topic, as it requires a computer to completely emulate a different computer with its own unique hardware and software. Many IT professionals and businesses rely heavily on various forms of virtualization, but the individual employees would be hard-pressed to explain how it works. Meltdown and Specter are related to this. |
| Critical: Under Linux 3.14.8 on System/390 in a UTC+14 time zone, a local user could potentially use a buffer overflow to change another user's default system clock from 12-hour to 24-hour. | This joke is about arcane systems that are running Linux in exceedingly unique situations, such that reproducing the error would be incredibly difficult or inconvenient, and would only affect a very tiny user base (if any at all). Other xkcd comics make references to such obscure computer-time issues relating to time zones and time conversions, and how many programmers find these issues frustrating or even traumatizing. UTC+14 is a time zone used only on some islands in the Pacific Ocean, i.e., the Line Islands, and is also the earliest time zone on earth. The joke continues by stating that even if all of these absurd conditions were met, the resulting vulnerability would still be relatively benign: simply changing a user's preferred clock display format. |
| x86 has way too many instructions. | The x86 architecture is considered "CISC" (a "complex instruction set computer"), having many instructions originally provided to make programming by a human simpler; other examples include the 68000 series used in the first Apple Mac. In the 1980s, this design philosophy was countered by the "RISC" ("reduced instruction set computer") design movement exemplified by SPARC, MIPS, PowerPC (previously used by Apple) and the ARM chips common in mobile phones - based on the observation that computer programs were increasingly generated by compilers (which only used a few instructions) rather than directly by people, and that the chip area dedicated to extra instructions could be better dedicated to, for example, cache. At the time, there was an internet war about the merits of each approach (with the Mac and PC being on different sides, at one time; owners of other competing systems such as the Archimedes and Amiga had similar arguments on usenet in the early 1990s); this "issue" may be posted by someone who still recalls these debates. Technically, the extra instructions do slightly complicate the task of validating correct chip behaviour and complicate the tool chains that manage software, which could be seen as a minor security risk; however, the 64-bit architecture introduced by AMD and since adopted by Intel does rationalise things somewhat, and all recent x86 chips break down instructions into RISC-like micro-operations, so the complication from a hardware perspective is localised. Recent security issues such as the speculative cache load issue in Meltdown and Spectre depend more on details of implementation rather than instruction set, and have been exhibited both by x86 (CISC) and ARM (RISC) processors. |
| NumPy 1.8.0 can factor primes in O(log n) time and must be quietly deprecated before anyone notices. | NumPy is the fundamental package for scientific computing with Python. If something can find the prime factors of a number this quickly, especially a semiprime with two large factors, there are attacks to break many crypto functions used in internet security. However, prime numbers have only a single factor, and "factoring primes" quickly is a simpler problem, that of proving that a number is in fact a prime. |
| Apple products grant remote access if you send them words that break the "I before E" rule. | Another joke on the first CVE and a common English writing rule of thumb, which fails almost as often as it succeeds. Possibly a jab at Apple's image, portraying their software as unable to handle improper grammar or spelling. |
| Skylake x86 chips can be pried from their sockets using certain flathead screwdrivers. | Skylake x86 chips are a line of microprocessors made by Intel. Yes, you can forcefully remove any processor from its socket with a screwdriver.[citation needed] There are many reports from people not using common sense. |
| Apparently Linus Torvalds can be bribed pretty easily. | Linus Torvalds is the benevolent dictator of the Linux kernel codebase. Normally it is hard to pass a change because he has the last word about what merge to the code base because that code is replicated in all Linux installations, but apparently he is easy to bribe, which would be a severe critical vulnerability to all Linux servers and machines. |
| An attacker can execute malicious code on their own machine and no one can stop them. | The point of an attack is to make someone else's machine perform actions against the owner's will. Anyone can make their own machine execute any code[citation needed], but this would usually not be described as an attack except in the case of a locked-down appliance, such as a video game console or pay TV decoder. |
| Apple products execute any code printed over a photo of a dog with a saddle and a baby riding it. | This could refer to a CVE vulnerability of JPG files where javascript embedded within the image file is executed by some application, only this time is in a printed photo instead of encoded into the image itself. |
| Under rare circumstances, a flaw in some versions of Windows could allow Flash to be installed. | Flash was discontinued because of its notoriously abysmal security record. All security experts advise against install. The joke here relates to the perceived difficulty with keeping Flash up to date or even installed properly to begin with. A common user experience which is the subject of numerous jokes and memes is the constant nagging notification to install or update Flash in order for web pages to display properly. While anecdotal, many IT professionals will bemoan the trouble that Flash has given them in the workplace due to these notifications and problems related to them. |
| Turns out the cloud is just other people's computers. | This refers to a computer meme where replace "cloud" with "other people's computers" must be used in all marketing presentation to CEOs and not computer literate persons to evaluate the security impact of using "Cloud services". Part of the humor here is that "the cloud", in actuality, is simply a term for hosted services, i.e., computers being run by other people (typically businesses that specialize in this type of "Platform As A Service" or "PAAS" service model). Calling "the cloud" as "other people's computers" is, at its core, entirely accurate, though it takes away the business jargon and simplifies the situation in such a way that it might cast doubt on the security, reliability, and general effectiveness of using "cloud" solutions. |
| A flaw in Mitre's CVE database allows arbitrary code insertion.[~~CLICK HERE FOR CHEAP VIAGRA~~] | Mitre's CVE database is the database where all CVE are stored. Attackers, after gaining access to the database via this flaw, add in a typical spam link purporting to offer cheap viagra. |
| It turns out Bruce Schneier is just two mischevious kids in a trenchcoat. | Appears in the title text. Bruce Schneier is security researcher and blogger. He was mentioned in the title texts of 748: Worst-Case Scenario and 1039: RuBisCO. The "two kids in a trenchcoat" is a reference to the Totem Pole Trench trope.
References
TranscriptLEAKED LIST OF MAJOR 2018 SECURITY VULNERABILITIES CVE-2018-????? Apple products crash when displaying certain Telugu or Bengali letter combinations. CVE-2018-????? An attacker can use a timing attack to extploit a race condition in garbage collection to extract a limited number of bits from the Wikipedia article on Claude Shannon. CVE-2018-????? At the cafe on Third Street, the Post-it note with the WiFi password is visible from the sidewalk. CVE-2018-????? A remote attacker can inject arbitrary text into public-facing pages via the comments box. CVE-2018-????? MySQL server 5.5.45 secretly runs two parallel databases for people who say "S-Q-L" and "sequel." CVE-2018-????? A flaw in some x86 CPUs could allow a root user to de-escalate to normal account privileges. CVE-2018-????? Apple products catch fire when displaying emoji with diacritics. CVE-2018-????? An oversight in the rules allows a dog to join a basketball team. CUE-2018-????? Haskell isn't side-effect-free after all; the effects are all just concentrated in this one. computer in Missouri that no one's checked on in a while. CVE-2018-????? Nobody really knows how hypervisors work. CVE-2018-????? Critical: Under Linux 3.14.8 on System/390 in a UTC+14 time zone, a local user could potentially use a buffer overflow to change another user's default system clock from 12-hour to 24-hour. CVE-2018-????? x86 has way too many instructions. CVE-2018-????? NumPy 1.8.0 can factor primes in O(log n) time and must be quietly deprecated before anyone notices. CVE-2018-????? Apple products grant remote access if you send them words that break the "I before E" rule. CVE-2018-????? Skylake x86 chips can be pried from their sockets using certain flathead screwdrivers. CVE-2018-????? Apparently Linus Torvalds can be bribed pretty easily. CVE-2018-????? An attacker can execute malicious code on their own machine and no one can stop them. CVE-2018-????? Apple products execute any code printed over a photo of a dog with a saddle and a baby riding it. CVE-2018-????? Under rare circumstances, a flaw in some versions of Windows could allow Flash to be installed. CVE-2018-????? Turns out the cloud is just other people's computers. CVE-2018-????? A flaw in Mitre's CVE database allows arbitrary code insertion.[~~CLICK HERE FOR CHEAP VIAGRA~~]
DiscussionFirst post!!!!!!!!!!!!!!!!!!!!!!!!!!! Anyway, the explanation looks like a train wreck, and I'm not sure if a rearranging it into a table or just adding bullet points to everything is better. I'm guessing that a table would be better, but I don't know how I can rearrange it. Can somebody help? Herobrine (talk) 06:35, 19 February 2018 (UTC)
Never ever have I heard anyone pronounce SQL as "sequel" - Is that a reqional dialect? 162.158.93.15 07:41, 19 February 2018 (UTC)
I want to take a moment to congratulate the dedication of whomever wrote the original explanation. Second languages are hard, bro. 108.162.215.10 07:48, 19 February 2018 (UTC) Has someone tried contacting Randall about "extploit"? If not, what would be the best way? Fabian42 (talk) 08:22, 19 February 2018 (UTC)
Regarding "Factor a prime": Factoring a prime is easy: The prime itself is the only factor, so it's sufficient to use AKS or whatever to check that. Public-key encryption relies on how hard it is to factor the product of two primes, which is a much harder problem. Maybe this is a typo in the comic? -- Comment Police (talk) (please sign your comments with ~~~~)
Can I edit some spelling errors? There seems to be some spelling errors here and there.Boeing-787lover 10:19, 19 February 2018 (UTC) I think the explanation of the one about injecting arbitrary text onto a page with the comments box is overthinking the joke. I think it really is just about the fact that you can write whatever you like in a comment. Look, I just hacked this page to display the word "penguin". Jeremyp (talk) 10:26, 19 February 2018 (UTC)
Since when is Bruce Schneier not real? 162.158.93.75 13:05, 19 February 2018 (UTC)
I've added some clarification to the "CRITICAL" item. I know there are several xkcd comics referencing similar problems but I unfortunately don't have the time to look them up, can someone do that and link them appropriately in the table? Domino (talk) 13:11, 19 February 2018 (UTC)domino
I think the article should start with an explanation of what is the CVE. From https://cve.mitre.org/ "CVE® is a list of entries—each containing an identification number, a description, and at least one public reference—for publicly known cybersecurity vulnerabilities. CVE Entries are used in numerous cybersecurity products and services from around the world, including the U.S. National Vulnerability Database (NVD)." - -- Comment Police (talk) (please sign your comments with ~~~~) "MySQL server 55.45" it is 5.5.45 if you zoom in a bit. 162.158.91.161 13:41, 19 February 2018 (UTC)Blocki "An attacker can execute malicious code on their own machine and no one can stop them" might be a jab at the trend toward more closed systems, where even the owner of a device is limited in what they can do on it.
It's my first comment here, so I may be wrong. I see the "CRITICAL" as a "differential” joke exhibiting that the requirement standards may be very different from a constructor to another. In fact, it seems that the apple’s bugs described here (crash, fire, remote access granted) are the mosst critical ones. The only two concerning Linux are the one labeled as critical and the one about bribery. I don’t know what to think about the almost complete absence of windows though. Feriaman. Could we get an Air Bud category? It seems to be a recurring theme in his comics. 162.158.246.88 18:50, 19 February 2018 (UTC)
Anyone happen to notice that instead of writing "mischievous," Randall opted for the non-standard spelling "mischevious?" The standard form would have been an I-before-E word... --162.158.88.164 00:45, 20 February 2018 (UTC) "Diacritics are the accents found on letters in some languages (eg. č, ģ ķ, ļ, ņ, š, ž). These would not be found on emojis." This misses the point. There is nothing that stops a unicode emoji being followed by unicode combining diacritical mark. The rendering engine does not have to display this in any particular way, but catching fire would be considered a bug by must users.[citation needed] 162.158.74.213 03:35, 20 February 2018 (UTC) "Flash was discontinued", really? Someone should tell Flash. And Facebook. I'm STILL experiencing issues on Facebook over their sloppy Flash programming interfering with my ability to watch Facebook videos (extra irritating as I'm sure my newly built computer is more powerful and capable than the computers owned by anyone I know, and certainly any phone or tablet, which don't experience these problems). And my last Flash update was a couple of weeks ago - seeing as this bug likes to include telling me I need to upgrade my Flash, even if I did so that day and Flash assures me I'm up date. NiceGuy1 (talk) 05:04, 20 February 2018 (UTC)
Timing Attack to exploit a race condition in garbage collection refers to Meltdown and Spectre CPU flaws that can be exploited in cloud server like the ones in Wikipedia. I don't think this is correct. Garbage collection is a technique of freeing up memory no longer used by a program, completely unrelated to speculative execution and the Spectre/Meltdown exploits... Jaalenja (talk) 07:34, 20 February 2018 (UTC) Apple products execute any code printed over a photo of a dog with a saddle and a baby riding it. ... This "bug" would not only require the device to figure out specifically what the photo contains image-wise, something that's REALLY HARD for computers to do reliably, it would also require OCR (Optical Character Recognition) type code to convert the text superimposed on the photo into executable code. In other words, it's hard to believe in 2018 that such a bug could exist. Maybe in the future when such things are more routine...? ... The funny thing is that I don't think it's beyond the realm of plausibility. Given the fact that modern operating systems try to index as much as possible, for faster searches, it seems logical that some OS (if not now, then in the future) would try to run OCR against every image and video in order to index whatever text it finds (much like how YouTube auto-generates captions by running speech-recognition over the entire soundtrack). Ditto for more generic image recognition to identify and index the picture content. A system that does this could easily end up with a bug (or back door) where certain kinds of image content result in an attempt to execute its OCR results as code. Shamino (talk) 15:03, 20 February 2018 (UTC) Does anyone think the 'I before E' could be a stab at Apple, in reference to Internet Explorer? -- Comment Police (talk) (please sign your comments with ~~~~) While it is true that part of the plot of the movie "Air Bud" was that there was nothing in the rules to prevent a dog joining a basketball team, I suspect that the recent attempt to run a dog as candidate for governor of Kansas was more on Randal's mind than a 20+ year old movie that (at most) a few million people saw when it was released.162.158.78.16 05:27, 22 February 2018 (UTC)
Is it just me, or does it feel like the "hack via edit box" thing feel like a reference to us? I mean, not only can this site be added to like that, it's the only one I know of and visit where you can do so without having an account. Seems perfect as the target of that particular one. :) NiceGuy1 (talk) 04:55, 23 February 2018 (UTC)
Is it notable that the bugs gradually become more and more trivial except where an Apple device is involved, where they progressively get both more worrying and more impossible to accomplish? 108.162.221.95 05:37, 23 March 2018 (UTC)
|
