416: Zealous Autoconfig
| Zealous Autoconfig |
 Title text: I hear this is an option in the latest Ubuntu release. |
Explanation[edit]
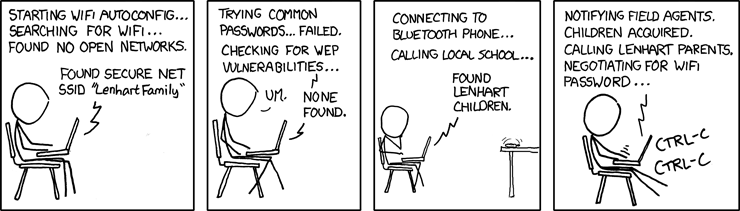
Cueball is seen in an attempt to connect his laptop to a Wi-Fi network using, as the comic title suggests, a particularly zealous "Wifi Autoconfig" utility — "zealous" being a synonym for "eager" or "enthusiastic." The utility manages to find a secure access point named "Lenhart Family," presumably Miss Lenhart's home Wi-Fi access point, and attempts to connect to it.
Instead of requesting a password, the program automatically begins a dictionary attack, entering in various commonly-used passwords in the hopes that Miss Lenhart has little regard for proper security measures (a flaw shared by many computer users). When this fails, the program attempts to exploit a WEP vulnerability, which surprises Cueball. This also fails, possibly because Miss Lenhart used WPA instead of WEP.
In the third panel, the autoconfig then connects to Cueball's Bluetooth phone and uses it to call a local school in order to locate the Lenhart children, who are attending there, and it reports that it has found them. It acts on this information in the fourth panel, notifying "field agents" to kidnap the Lenhart children for nonmonetary ransom, and then reports that the children are acquired (very fast it seems). With the children as hostages, the program begins negotiations with the parents, offering their safe return in exchange for the Wi-Fi password.
This puns on the computing sense of "negotiation": network protocols (such as HTTP) often specify routines whereby a server and a client computer can agree on the best format in which data can be transferred. This is called content negotiation or format negotiation (see for example section 3.4 of the specification for "semantics and content" in HTTP).
Cueball, frightened by these actions, repeatedly presses Ctrl+C in an attempt to cancel the process, with little success. Ctrl+C is used to abort programs started from a terminal (Unix/Linux) or a command line prompt (cmd.exe under Windows). (The alternative use of Ctrl+C in many programs, as a shortcut for copying a text selection, is probably not what Cueball has in mind at this point.) Part of the humor is that he only attempts to cancel quite late in the process, well after (for instance) the school was first called, probably because of a morbid curiosity to see what happens.
The title text mentions Ubuntu, a Linux distribution that attempts to be as user-friendly as possible. Randall mentions that he has heard that this "user-friendly" Zealous Autoconfig option has already been installed in the latest Ubuntu release.
Problems that arise when you leave decisions to a computer program are also explored in depth in comic 1619: Watson Medical Algorithm.
Transcript[edit]
- [Cueball is sitting on a chair with his laptop in his lap. The text written on the laptop is shown above him, and there is a zigzag line from the laptop to the bottom of the last sentence.]
- Laptop: Starting WiFi autoconfig... searching for WiFi... Found no open networks.
- Laptop: Found secure net SSID "Lenhart Family"
- [Same setup, but Cueball has changed position. This time there are two zigzag lines between the two sentences from the laptop.]
- Laptop: Trying common passwords... Failed. Checking for WEP Vulnerabilities...
- Cueball: Um.
- Laptop: None found.
- [Cueball is still sitting with laptop in his lap, but his hand is on his chin, or perhaps covering his mouth in shock. A phone on table across room starts vibrating. Again, there is only one zigzag line to the bottom sentence from the laptop.]
- Laptop: Connecting to Bluetooth phone... Calling local school...
- Laptop: Found Lenhart children.
- [Zoom back to Cueball, who is furiously typing on his laptop, legs stretched out.]
- Laptop: Notifying field agents. Children acquired. Calling Lenhart parents. Negotiating for WiFi password...
- Cueball [typing] on laptop: Ctrl-C Ctrl-C
Discussion
I have my network autoconfig set up to run a rainbow table attack if there's a password on the network. Wifi everywhere is great. Davidy22(talk) 15:05, 1 November 2012 (UTC)
- That's superb! Suspender guy (talk) 17:12, 22 December 2015 (UTC)
- Do you have that rainbow table somewhere? Wifi everywhere is great. PoolloverNathan[talk]U•T•S•c 17:59, 24 April 2023 (UTC)
But how would the school know about the Lenhart children if Mrs. Roberts deleted the students table? 184.11.73.88 (talk) (please sign your comments with ~~~~)}
- I say it'd be a liveware attack. A voice-call from the application, with in-built speech-synthisis and speech-recognition capabilities, requesting information from the school secretary him/herself. Probably a Black Hat construction. Or Hartigan (/whoever) from the Leverage series... ;) 178.107.249.215 23:43, 17 June 2013 (UTC)
I think Miss Lenhart must be the Lenhart children's paternal aunt. Their mother is most probably Mrs. Lenhart. Xhfz (talk) 02:20, 14 October 2013 (UTC)
When I saw "Ctrl + C" my first thought was "copy." It's the dumb thing about windows and every implementation that uses that. 108.162.245.217 14:02, 9 July 2014 (UTC)
It gets worse! I regularly use Konsole, where ctrl-c cancels things; ctrl-shift-c copies, but then I start using ctrl-shift-c in Chrome and end up debugging web pages instead of copying text. GAH! 141.101.70.157 (talk) (please sign your comments with ~~~~)
huh i once was playing kol clicked something and ended up with tons of php in my screen An user who has no account yet (talk) 17:41, 6 September 2023 (UTC)
A similar concept to 538: Security. Shanek (talk) 12:29, 1 May 2015 (UTC)
Believe it or not, you can use ctrl-insert to copy on almost any linux or windows program. Shift-delete is cut and shift-insert is paste. --PsyMar (talk) 13:13, 1 May 2015 (UTC)
- I think the difference is WordPerfect vs Word short-cuts, both are supported both for historic reason and to support both left and right handed users with a mouse in their primary hand.162.158.133.114 01:45, 23 December 2015 (UTC)
- XKCD 1479 right here.108.162.237.124 17:49, 9 May 2015 (UTC)
