2531: Dark Arts
| Dark Arts |
 Title text: You think, 'okay, THIS is an ideal use case for hardlinks!' but then 6 months later you're doing some extremely cursed Google search like 'javascript ext4' and wondering where things went wrong. |
Explanation[edit]
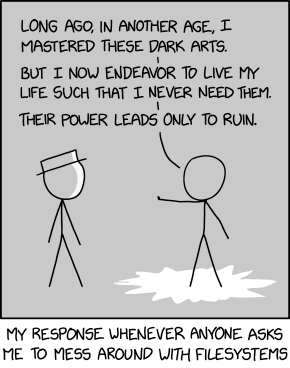
White Hat has presumably just asked Cueball to perform some task involving filesystems. Cueball responds with an exceptionally melodramatic monologue, referring to the subject as "dark arts" and stating he'd rather not have anything to do with them. This is reminiscent of a fairly typical scene in fantasy novels, superhero movies, etc: a person with supernatural powers explains they prefer not to use them, as their use is likely to have negative effects that outweigh the positive ones. Often this is tied to a tragic backstory of the character, where the use of their powers previously caused them or someone close to them much suffering.
The humor of the comic comes from the parallel drawn; it seems unlikely that knowledge of filesystems could have negative consequences on the scale of, say, leveling a city, so the comparison is hyperbolic. However, much of today's infrastructure does depend on legacy systems that can be very overly complex to work with, having weathered aggressive political conflicts and short corporate deadlines for decades now. An example is the recent shutdown of the pgp keyserver network, or how the developer of the fastest linux filesystem built (reiserfs) was imprisoned for murdering his wife right before it could be merged into linux. Still, this joke is in a similar vein to comics like 349: Success, in which Cueball's relationship with technology is shown to have a potential for disaster far exceeding that of a normal person's.
A filesystem is the part of a computer's operating system that handles the organization of data in persistent storage, usually splitting it into files and directories. It can be a very complicated piece of software. Because of this, it is easy to make mistakes in advanced usage, and because it controls practically all data on a given machine, mistakes made can have serious consequences (e.g., loss of data). These properties of filesystems are likely why Cueball is reluctant to mess with them.
ext4 is a popular filesystem used with the Linux operating system kernel.
Hardlinks allow two filenames to refer to the same underlying file or directory. These can be particularly tricky to use, as in nearly all respects they look like regular files, but modifying them can have effects that are not immediately obvious (e.g., changing what one filename refers to, the other will not remain consistent). Hardlinks and their misuse have been referenced in xkcd before, as in 981: Porn Folder.
The title text hints at an experience Cueball or Randall had (his own "tragic backstory", if you will), involving hardlinks on ext4. He thought he had found an ideal use case for them, one which presumably avoided most of their pitfalls, but still, six months later, ended up having to troubleshoot some inscrutable bug arising from his decision.
Javascript is a programming language most often associated with web pages. As such it is not usually interacting directly with a computer's filesystem, since allowing arbitrary websites to access the filesystem is widely considered an extremely bad idea.[citation needed] It is possible to run Javascript directly outside of a browser – in which case it does have access to common filesystem operations, and even theoretically to the internals of the filesystem – but since it is a high-level language with poor support for working with the data structures a filesystem uses, this would be a painful, "cursed" way to go about things.
A senior IT professional (nowadays fewer people need to know about such features) will be reminded of their own experiences and mishaps with non-trivial file system configurations. Beyond hardlinks, filesystems may have a number of features a normal user or even an admin are not aware of. Such features are prone to bugs, poor documentation, or poor integration with other system tools. For example:
- Symbolic links (soft links) - one file links to another using its name. While symbolic links work "everywhere," hardlinks are generally limited.
- Compressed filesystems can cause unexpected side effects in performance, quota management, and disk fragmentation.
- Sparse files and shallow copies (copy on demand).
- Live filesystem backup and file locking.
- Read-only filesystems.
- 'Virtual' filesystems, like memory-backed and file-backed file systems, backed by dynamic data or databases.
- 'Overlay' file systems where a read-only portion is overlaid and partially shadowed by another file system.
- File caching for read or write operation.
- Syncing file systems.
- Many, many more.
"In another age" might refer to the fact that detailed file system manipulations were common in the days when developers were installing, configuring and managing operating systems and software on physical servers. When disk space was limited and network speeds were low, such manipulations saved space and time. Virtualization, containerization and deployment frameworks isolate developers and administrators from such low level details.
Transcript[edit]
- [Cueball and White Hat stand in a slightly darkened room, with a jagged circle of light centered on Cueball and light-reflecting onto White Hat's face. Cueball holds his arm out with his palm facing towards White Hat.]
- Cueball: Long ago, in another age, I mastered these dark arts.
- Cueball: But I now endeavor to live my life such that I never need them.
- Cueball: Their power leads only to ruin.
- [Caption below panel]
- My response whenever anyone asks me to mess around with filesystems
Discussion
Whoo, my first "first explanation". It's not a particularly thorny comic but my explanation could still use some judicious editing I'm sure. Esogalt (talk) 06:51, 21 October 2021 (UTC)
I added a "citation needed" to the claim that letting arbitrary websites modify your filesystem is a Bad Idea, because I couldn't resist >.< 172.68.132.74 08:40, 21 October 2021 (UTC)
- [citation needed] 162.158.88.113 10:45, 21 October 2021 (UTC)
The previous comment is almost worth an XKCD comic of its own. --162.158.203.24 10:10, 21 October 2021 (UTC)
WTH did Randal do that lead him to put ext4 and javascript in the same search, and why does he think hardlinks are the problem with such a cursed search? 172.69.69.182 10:17, 21 October 2021 (UTC)
Which specific IT professional is the explanation referring to? 141.101.105.35 12:40, 21 October 2021 (UTC)
- None in particular, just in general. 172.69.90.11 14:01, 21 October 2021 (UTC)
- It's an expression. It's essentially the same as saying "Any experienced IT professional", but a little more stylistic. That whole sentence seems slightly gatekeeper-ish to me anyway. Esogalt (talk) 13:51, 21 October 2021 (UTC)
As an added wrinkle, the alt text's search is cursed because there is a javascript framework completely unrelated to the ext filesystem that is also called ext, which had a version 4 and would thus muddy the waters of the search. -- 172.70.178.51 13:15, 21 October 2021 (UTC)
- Explanation should include why the alt text's search is "cursed." Seems like this comment hints at it, but I don't know enough about the topic to know if that is the full curse. 162.158.107.234 17:22, 21 October 2021 (UTC)
- See also filesystem driver for node.js with a warning that it will fail if the device capacity exceeds 8192 Terabytes due to Javascript way to represent integers. Alexcohn (talk) 06:48, 26 October 2021 (UTC)
XKCD and its weirdly fitting timing in relation to my life again… Just 4 hours earlier, I had dealt with hardlinks in a Bash script and produced things like cd "$(readlink -f "$(pwd)")". Fabian42 (talk) 13:53, 21 October 2021 (UTC)
I believe that Microsoft's implementation of OneDrive is cursed by evil intention. The intention (and default behavior) is to keep the actual file contents in the cloud with nothing but a reference on the machine in my control. The presumed benefit is that it is easy to have the files available on any machine the user logs into ... because they aren't really on the machine at all. Other perceived benefit is it saves space on the local machine. The evil consequence is that files are unavailable when the machine is offline. My opinion is that most users almost never need their OneDrive files on anything but their primary machine, and would be pretty sore if the files in the cloud got wiped out with no backup on their primary machine. I presume that most people view the files on their machine as primary and view the cloud copies as their backup. Rtanenbaum (talk) 22:23, 21 October 2021 (UTC)
- And don't forget that Microsoft will definitely search through the stuff you stored on OneDrive. You may find out that something you stored was declared dangerous by them and deleted ... -- Hkmaly (talk) 02:36, 22 October 2021 (UTC)
I don't think there is anything dark or problematic on most stuff mentioned in the article. And they generally work without problems on Linux. On the other hand, in most of movies where hero says something like this I think he's chicken-hearted coward and the mentioned dark arts is cool think I would like to know. So, maybe I'm just already on dark side. -- Hkmaly (talk) 02:36, 22 October 2021 (UTC)
File Systems! GRRRR!! File Systems Management was the class that kept me from getting a 4.0 GPA while getting my degree in Computer Science. Oh well, I was probably doing only C work, so I was happy to get the B. That was a long time ago, and I wound up not doing anything at all involved with programming or anything else related to Computer Science.... 172.70.130.87 11:09, 22 October 2021 (UTC)
I use game mod managers that use hard links frequently. Never had a problem with those, but as that is below-the-hood, it might not count. My problems with partition tables as a dual booter, including cloning, boot records etc, have been far worse. 141.101.105.47 17:34, 22 October 2021 (UTC)
- This was the way every smart admin managed software updates on servers in the days when disk space was measured in MegaBytes and the network was a 10MB/s shared token ring --162.158.159.17 18:40, 22 October 2021 (UTC)
So I feel like this comic has something to do with this study : https://linustechtips.com/topic/1375321-report-suggests-many-gen-z-students-do-not-know-how-to-use-a-basic-file-directory/ J (talk) 10:33, 6 November 2021 (UTC)
Cursed[edit]
I've thought this before (not sure if I ever wrote it anywhere, perhaps I did in the now long-deceased fora), but given the reappearance of 'cursed'ness in fairly recent comics, there maybe should be a Cursed category (of which Category:Cursed Connectors, recently created for a close run of four items, would obviously be a subset, if not members in their own right). Cursedicity seems to be a recurring Munroe meme (I counted more than a dozen distinct examples from a quick search), so consider this a suggestion. For all things mentioned/depicted/contemplated as cursed. 141.101.98.199 19:16, 21 October 2021 (UTC)
Examples[edit]
Are there some examples to give of characters with great powers that they don't use because reasons? Perhaps a TV Tropes page or three in this area? I actually wondered if the dialogue in this xkcd was mostly a direct quote from something. Start with these maybe. But I'm hoping that someone recognises a scene. https://tvtropes.org/pmwiki/pmwiki.php/Main/RetiredBadass https://tvtropes.org/pmwiki/pmwiki.php/Main/DangerousForbiddenTechnique
The first found from "Obi-Wan Kenobi", who appears to be a crazy hermit although later it's established that he lives on Tatooine specifically to protect Luke Skywalker, secretly. The second, found from the first. But halfway down "Dangerous techniques", I haven't found an example that precisely fits this comic. I did skip the "anime and manga" entries, which are said to be many. Oh, wait: under Literature, "Babylon 5" (spin off books evidently) mentions a telepath interrogating someone by mind reading when they are dying or brain dead. That is unhealthy, and actually does correspond to some scenarios of struggling with data filesystems: rescuing data from a dead disk. 141.101.107.43 11:29, 22 October 2021 (UTC) Robert Carnegie [email protected]
- Non-mystical examples I thought of were CPO Ryback (Under Siege, though not so much regretting past expertise as intending to settle back into 'normal' trivial service until forced) or John Rambo (First Blood, pushed too far by an unlucky sadist ignorant of the nature of the dragon he was poking at). For "You're messing with forces you do jot understand" I was thinking more Indianna Jones (having witnessed, and expected shortly in advance, the Nazis' and collaborator's demise, he would have been concerned about the safety of Top Men if he believed there were any).
- I haven't yet gone to the TVTs site links, as that way lies similar dangers</inMyPortentousVoice!> that I'm reluctant to reawaken, but arcane and ancient knowledge is always ripe for meddling with by an upstart, with elderly mentors who are the (surviving) past-meddlers generally being the voice of caution (rightly or wrongly, according to how the plot should twist - depends if the Upstart is the One Who Was Prophecised But Nobody Knows It, or not) and perhaps even the (ultimately ineffective?) Guardian Of The Thing whether that's a ring or tome or a mystical stone. 141.101.107.29 15:02, 22 October 2021 (UTC)
Relatable comic[edit]
This is actually how I feel whenever someone asks for help dealing with proprietary software or hardware. Remote functionality that could be local, service which supplants intrinsic functionality, wireless for devices that don't wander (looking at you, bike shifters), trust in place of secure practice, gimmicks used to distract from downgraded end-user agency, downgrades pushed as security\simplification, these are things that drove me away from modern computing, 'smart'phones, automobiles, & other mass-market junk of today. The whole market of consumer goods & services is full of bad practices, & bad practices are contagious. Now when someone asks me "do you work with computers" I shake my head & toss up my hands & say "I try not to." ProphetZarquon (talk) 14:26, 22 October 2021 (UTC)
So relatable. Today I had to type mount -o remount,rw /dev/sda1 / into a single user shell, which I'm pretty sure I hadn't been in this entire millennium, because I forgot my stupid password that I haven't even had to use for at least a year, and now I can't sleep. 172.68.132.114 06:08, 23 October 2021 (UTC)
Arts scrambled[edit]
You guys, I just realized that "Arts" scrambled so that the letters S-T are at the start is "star", therefore making this comic title "Dark Star," an ancient entity last seen in a Super Mario Bros. RPG. I don't know if this is a coincidence or what, but it's WEIRD. Z1mp0st0rz (talk) 17:11, 24 April 2024 (UTC)
- "Dark Star" is many things, several of which are at least as likely... 141.101.99.136 18:32, 24 April 2024 (UTC)
 Add comment
Add comment
